Tady je log z RogueKiller - Tady už asi nějaký problém ale bude, vidím nějaké ERRORY
 ==============================LOG=====================================
==============================LOG=====================================RogueKiller V8.8.15 _x64_ [Mar 27 2014] by Adlice Software
mail :
http://www.adlice.com/contact/Podpora :
http://forum.adlice.comWebové stránky :
http://www.adlice.com/softwares/roguekiller/ :
http://www.adlice.comOperační systém : Windows 8.1 (6.3.9200 ) 64 bits version
Spuštěno v : Normální režim
Uživatel : Ivo [Práva správce]
Mód : Kontrola -- Datum : 05/01/2014 21:01:56
| ARK || FAK || MBR |
¤¤¤ Škodlivé procesy: : 1 ¤¤¤
[SUSP UNIC] OpaqueTaskbar.exe -- D:\Dokumenty\WINDOWS-8-NEPR�?HLEDNÝ,HLAVNÍ-PANEL\OpaqueTaskbar.exe [-] -> SMAZÁNO [TermProc]
¤¤¤ ¤¤¤ Záznamy Registrů: : 6 ¤¤¤
[RUN][SUSP UNIC] HKCU\[...]\Run : OpaqueTaskbar ("D:\Dokumenty\WINDOWS-8-NEPR�?HLEDNÝ,HLAVNÍ-PANEL\OpaqueTaskbar.exe" /resident [-]) -> NALEZENO
[RUN][SUSP UNIC] HKUS\S-1-5-21-3425194565-27084353-826121341-1001\[...]\Run : OpaqueTaskbar ("D:\Dokumenty\WINDOWS-8-NEPR�?HLEDNÝ,HLAVNÍ-PANEL\OpaqueTaskbar.exe" /resident [-]) -> NALEZENO
[HJ POL][PUM] HKCU\[...]\System : DisableTaskMgr (0) -> NALEZENO
[HJ POL][PUM] HKCU\[...]\System : DisableRegistryTools (0) -> NALEZENO
[HJ DESK][PUM] HKLM\[...]\NewStartPanel : {59031a47-3f72-44a7-89c5-5595fe6b30ee} (1) -> NALEZENO
[HJ DESK][PUM] HKLM\[...]\NewStartPanel : {20D04FE0-3AEA-1069-A2D8-08002B30309D} (1) -> NALEZENO
¤¤¤ naplánované úlohy : 0 ¤¤¤
¤¤¤ spuštění položky : 0 ¤¤¤
¤¤¤ Webové prohlížeče : 0 ¤¤¤
¤¤¤ Browser Addons : 0 ¤¤¤
¤¤¤ Zvláštní soubory / Složky: ¤¤¤
¤¤¤ Ovladač : [NENAHRÁNO 0x0] ¤¤¤
[Address] IAT @explorer.exe (SetWindowPos) : USER32.dll -> HOOKED (C:\Program Files (x86)\IObit\Start Menu 8\StartMenuDll64.dll @ 0x004255C0)
[Address] EAT @explorer.exe (DllCanUnloadNow) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD274C)
[Address] EAT @explorer.exe (DllGetClassObject) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD4984)
[Address] EAT @explorer.exe (DwmAttachMilContent) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD8180)
[Address] EAT @explorer.exe (DwmDefWindowProc) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD2C30)
[Address] EAT @explorer.exe (DwmDetachMilContent) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD8180)
[Address] EAT @explorer.exe (DwmEnableBlurBehindWindow) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD2A70)
[Address] EAT @explorer.exe (DwmEnableComposition) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBDC60C)
[Address] EAT @explorer.exe (DwmEnableMMCSS) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD3788)
[Address] EAT @explorer.exe (DwmExtendFrameIntoClientArea) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD2DC0)
[Address] EAT @explorer.exe (DwmFlush) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD26C0)
[Address] EAT @explorer.exe (DwmGetColorizationColor) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBDC118)
[Address] EAT @explorer.exe (DwmGetCompositionTimingInfo) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD1D40)
[Address] EAT @explorer.exe (DwmGetGraphicsStreamClient) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD8180)
[Address] EAT @explorer.exe (DwmGetGraphicsStreamTransformHint) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD8180)
[Address] EAT @explorer.exe (DwmGetTransportAttributes) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBDC8B0)
[Address] EAT @explorer.exe (DwmGetWindowAttribute) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD1010)
[Address] EAT @explorer.exe (DwmInvalidateIconicBitmaps) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD6308)
[Address] EAT @explorer.exe (DwmIsCompositionEnabled) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD11B0)
[Address] EAT @explorer.exe (DwmModifyPreviousDxFrameDuration) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBDD050)
[Address] EAT @explorer.exe (DwmQueryThumbnailSourceSize) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD6F34)
[Address] EAT @explorer.exe (DwmRegisterThumbnail) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD69A8)
[Address] EAT @explorer.exe (DwmRenderGesture) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD7CEC)
[Address] EAT @explorer.exe (DwmSetDxFrameDuration) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBDD050)
[Address] EAT @explorer.exe (DwmSetIconicLivePreviewBitmap) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBDD1CC)
[Address] EAT @explorer.exe (DwmSetIconicThumbnail) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBDD558)
[Address] EAT @explorer.exe (DwmSetPresentParameters) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBDD050)
[Address] EAT @explorer.exe (DwmSetWindowAttribute) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD10E8)
[Address] EAT @explorer.exe (DwmShowContact) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD3A90)
[Address] EAT @explorer.exe (DwmTetherContact) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBDCB1C)
[Address] EAT @explorer.exe (DwmTransitionOwnedWindow) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBDDBD8)
[Address] EAT @explorer.exe (DwmUnregisterThumbnail) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD677C)
[Address] EAT @explorer.exe (DwmUpdateThumbnailProperties) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD3A10)
[Address] EAT @explorer.exe (DwmpAllocateSecurityDescriptor) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD2320)
[Address] EAT @explorer.exe (DwmpDxGetWindowSharedSurface) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD5FE0)
[Address] EAT @explorer.exe (DwmpDxUpdateWindowSharedSurface) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD7710)
[Address] EAT @explorer.exe (DwmpDxgiIsThreadDesktopComposited) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD3760)
[Address] EAT @explorer.exe (DwmpFreeSecurityDescriptor) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBD22E4)
[Address] EAT @explorer.exe (DwmpRenderFlick) : DUI70.dll -> HOOKED (C:\WINDOWS\SYSTEM32\dwmapi.dll @ 0x6CBDCE70)
[Address] EAT @explorer.exe (DllCanUnloadNow) : BatMeter.dll -> HOOKED (C:\WINDOWS\SYSTEM32\PhotoMetadataHandler.dll @ 0x5FF31010)
[Address] EAT @explorer.exe (DllGetClassObject) : BatMeter.dll -> HOOKED (C:\WINDOWS\SYSTEM32\PhotoMetadataHandler.dll @ 0x5FF31E60)
[Address] EAT @explorer.exe (DllRegisterServer) : BatMeter.dll -> HOOKED (C:\WINDOWS\SYSTEM32\PhotoMetadataHandler.dll @ 0x5FF730B0)
[Address] EAT @explorer.exe (DllUnregisterServer) : BatMeter.dll -> HOOKED (C:\WINDOWS\SYSTEM32\PhotoMetadataHandler.dll @ 0x5FF73114)
[Address] EAT @explorer.exe (GetAsymmetricEncryptionInterface) : sxs.dll -> HOOKED (C:\WINDOWS\SYSTEM32\bcryptPrimitives.dll @ 0x6E5A9A20)
[Address] EAT @explorer.exe (GetCipherInterface) : sxs.dll -> HOOKED (C:\WINDOWS\SYSTEM32\bcryptPrimitives.dll @ 0x6E5BDDC8)
[Address] EAT @explorer.exe (GetHashInterface) : sxs.dll -> HOOKED (C:\WINDOWS\SYSTEM32\bcryptPrimitives.dll @ 0x6E5ABD44)
[Address] EAT @explorer.exe (GetKeyDerivationInterface) : sxs.dll -> HOOKED (C:\WINDOWS\SYSTEM32\bcryptPrimitives.dll @ 0x6E5CD880)
[Address] EAT @explorer.exe (GetRngInterface) : sxs.dll -> HOOKED (C:\WINDOWS\SYSTEM32\bcryptPrimitives.dll @ 0x6E5A3C14)
[Address] EAT @explorer.exe (GetSecretAgreementInterface) : sxs.dll -> HOOKED (C:\WINDOWS\SYSTEM32\bcryptPrimitives.dll @ 0x6E5B516C)
[Address] EAT @explorer.exe (GetSignatureInterface) : sxs.dll -> HOOKED (C:\WINDOWS\SYSTEM32\bcryptPrimitives.dll @ 0x6E5B4FFC)
[Address] EAT @explorer.exe (ProcessPrng) : sxs.dll -> HOOKED (C:\WINDOWS\SYSTEM32\bcryptPrimitives.dll @ 0x6E5A12D0)
[Address] EAT @explorer.exe (AsyncGetClassBits) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EB70B0)
[Address] EAT @explorer.exe (AsyncInstallDistributionUnit) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EB7210)
[Address] EAT @explorer.exe (BindAsyncMoniker) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA1F90)
[Address] EAT @explorer.exe (CDLGetLongPathNameA) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EB78D0)
[Address] EAT @explorer.exe (CDLGetLongPathNameW) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EB78E8)
[Address] EAT @explorer.exe (CORPolicyProvider) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA1674)
[Address] EAT @explorer.exe (CoGetClassObjectFromURL) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EB73FC)
[Address] EAT @explorer.exe (CoInstall) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EB7460)
[Address] EAT @explorer.exe (CoInternetCanonicalizeIUri) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E65660)
[Address] EAT @explorer.exe (CoInternetCombineIUri) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E680A0)
[Address] EAT @explorer.exe (CoInternetCombineUrl) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E546A4)
[Address] EAT @explorer.exe (CoInternetCombineUrlEx) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E543C0)
[Address] EAT @explorer.exe (CoInternetCompareUrl) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA5280)
[Address] EAT @explorer.exe (CoInternetCreateSecurityManager) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E21EE0)
[Address] EAT @explorer.exe (CoInternetCreateZoneManager) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E30810)
[Address] EAT @explorer.exe (CoInternetFeatureSettingsChanged) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EE0284)
[Address] EAT @explorer.exe (CoInternetGetProtocolFlags) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA537C)
[Address] EAT @explorer.exe (CoInternetGetSecurityUrl) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA53D0)
[Address] EAT @explorer.exe (CoInternetGetSecurityUrlEx) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E69CD0)
[Address] EAT @explorer.exe (CoInternetGetSession) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E22460)
[Address] EAT @explorer.exe (CoInternetIsFeatureEnabled) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E68DC0)
[Address] EAT @explorer.exe (CoInternetIsFeatureEnabledForIUri) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E651B8)
[Address] EAT @explorer.exe (CoInternetIsFeatureEnabledForUrl) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E61820)
[Address] EAT @explorer.exe (CoInternetIsFeatureZoneElevationEnabled) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA586C)
[Address] EAT @explorer.exe (CoInternetParseIUri) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E556A8)
[Address] EAT @explorer.exe (CoInternetParseUrl) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E31490)
[Address] EAT @explorer.exe (CoInternetQueryInfo) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E67C50)
[Address] EAT @explorer.exe (CoInternetSetFeatureEnabled) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA5AF4)
[Address] EAT @explorer.exe (CompareSecurityIds) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E3D1A4)
[Address] EAT @explorer.exe (CompatFlagsFromClsid) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E64044)
[Address] EAT @explorer.exe (CopyBindInfo) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EB3020)
[Address] EAT @explorer.exe (CopyStgMedium) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E2BA0C)
[Address] EAT @explorer.exe (CreateAsyncBindCtx) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E786C0)
[Address] EAT @explorer.exe (CreateAsyncBindCtxEx) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E63D14)
[Address] EAT @explorer.exe (CreateFormatEnumerator) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E468E0)
[Address] EAT @explorer.exe (CreateIUriBuilder) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E23660)
[Address] EAT @explorer.exe (CreateURLMoniker) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E7CCF4)
[Address] EAT @explorer.exe (CreateURLMonikerEx) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E278D0)
[Address] EAT @explorer.exe (CreateURLMonikerEx2) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E640F0)
[Address] EAT @explorer.exe (CreateUri) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E216F0)
[Address] EAT @explorer.exe (CreateUriFromMultiByteString) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA1EE4)
[Address] EAT @explorer.exe (CreateUriPriv) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA1EF8)
[Address] EAT @explorer.exe (CreateUriWithFragment) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA1F40)
[Address] EAT @explorer.exe (DllCanUnloadNow) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E21600)
[Address] EAT @explorer.exe (DllGetClassObject) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E6AB3C)
[Address] EAT @explorer.exe (DllInstall) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA2458)
[Address] EAT @explorer.exe (DllRegisterServer) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA2464)
[Address] EAT @explorer.exe (DllRegisterServerEx) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E7E070)
[Address] EAT @explorer.exe (DllUnregisterServer) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA2470)
[Address] EAT @explorer.exe (Extract) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EB7F74)
[Address] EAT @explorer.exe (FaultInIEFeature) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EB8FE8)
[Address] EAT @explorer.exe (FileBearsMarkOfTheWeb) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E56B60)
[Address] EAT @explorer.exe (FindMediaType) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA2E9C)
[Address] EAT @explorer.exe (FindMediaTypeClass) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E46080)
[Address] EAT @explorer.exe (FindMimeFromData) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E650BC)
[Address] EAT @explorer.exe (GetAddSitesFileUrl) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EE02B0)
[Address] EAT @explorer.exe (GetClassFileOrMime) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E7B8EC)
[Address] EAT @explorer.exe (GetClassURL) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA2074)
[Address] EAT @explorer.exe (GetComponentIDFromCLSSPEC) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EB92E8)
[Address] EAT @explorer.exe (GetIDNFlagsForUri) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E3C7F0)
[Address] EAT @explorer.exe (GetIUriPriv) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA1F60)
[Address] EAT @explorer.exe (GetIUriPriv2) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA1F50)
[Address] EAT @explorer.exe (GetLabelsFromNamedHost) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EE8B54)
[Address] EAT @explorer.exe (GetMarkOfTheWeb) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED9390)
[Address] EAT @explorer.exe (GetPortFromUrlScheme) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA1E94)
[Address] EAT @explorer.exe (GetPropertyFromName) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA1EA4)
[Address] EAT @explorer.exe (GetPropertyName) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA1EB4)
[Address] EAT @explorer.exe (GetSoftwareUpdateInfo) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E7E070)
[Address] EAT @explorer.exe (GetUrlmonThreadNotificationHwnd) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E7DEB4)
[Address] EAT @explorer.exe (GetZoneFromAlternateDataStreamEx) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E26D90)
[Address] EAT @explorer.exe (HlinkGoBack) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED6E78)
[Address] EAT @explorer.exe (HlinkGoForward) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED6F24)
[Address] EAT @explorer.exe (HlinkNavigateMoniker) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED6FD0)
[Address] EAT @explorer.exe (HlinkNavigateString) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED7004)
[Address] EAT @explorer.exe (HlinkSimpleNavigateToMoniker) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED7038)
[Address] EAT @explorer.exe (HlinkSimpleNavigateToString) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED75E8)
[Address] EAT @explorer.exe (IECompatLogCSSFix) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EB12FC)
[Address] EAT @explorer.exe (IEDllLoader) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA26F0)
[Address] EAT @explorer.exe (IEGetUserPrivateNamespaceName) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EB3244)
[Address] EAT @explorer.exe (IEInstallScope) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EB7554)
[Address] EAT @explorer.exe (IntlPercentEncodeNormalize) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA1F70)
[Address] EAT @explorer.exe (IsAsyncMoniker) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E621FC)
[Address] EAT @explorer.exe (IsDWORDProperty) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA1EC4)
[Address] EAT @explorer.exe (IsIntranetAvailable) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EE0668)
[Address] EAT @explorer.exe (IsJITInProgress) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E3B328)
[Address] EAT @explorer.exe (IsLoggingEnabledA) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED855C)
[Address] EAT @explorer.exe (IsLoggingEnabledW) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED8688)
[Address] EAT @explorer.exe (IsStringProperty) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA1ED4)
[Address] EAT @explorer.exe (IsValidURL) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E57610)
[Address] EAT @explorer.exe (MkParseDisplayNameEx) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E792F0)
[Address] EAT @explorer.exe (ObtainUserAgentString) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EADCE0)
[Address] EAT @explorer.exe (PrivateCoInstall) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EB7560)
[Address] EAT @explorer.exe (QueryAssociations) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E3E9C0)
[Address] EAT @explorer.exe (QueryClsidAssociation) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EB0A8C)
[Address] EAT @explorer.exe (RegisterBindStatusCallback) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E5F600)
[Address] EAT @explorer.exe (RegisterFormatEnumerator) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E61C6C)
[Address] EAT @explorer.exe (RegisterMediaTypeClass) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA20C0)
[Address] EAT @explorer.exe (RegisterMediaTypes) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA2210)
[Address] EAT @explorer.exe (RegisterWebPlatformPermanentSecurityManager) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E58C54)
[Address] EAT @explorer.exe (ReleaseBindInfo) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E27D40)
[Address] EAT @explorer.exe (RevokeBindStatusCallback) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E5FBF0)
[Address] EAT @explorer.exe (RevokeFormatEnumerator) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA22CC)
[Address] EAT @explorer.exe (SetAccessForIEAppContainer) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EB3258)
[Address] EAT @explorer.exe (SetSoftwareUpdateAdvertisementState) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E7E070)
[Address] EAT @explorer.exe (ShouldDisplayPunycodeForUri) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EADE50)
[Address] EAT @explorer.exe (ShouldShowIntranetWarningSecband) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E63A3C)
[Address] EAT @explorer.exe (ShowTrustAlertDialog) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EE0820)
[Address] EAT @explorer.exe (URLDownloadA) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA5CC4)
[Address] EAT @explorer.exe (URLDownloadToCacheFileA) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED7D9C)
[Address] EAT @explorer.exe (URLDownloadToCacheFileW) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E4A0C4)
[Address] EAT @explorer.exe (URLDownloadToFileA) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED7F10)
[Address] EAT @explorer.exe (URLDownloadToFileW) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E4EFD0)
[Address] EAT @explorer.exe (URLDownloadW) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA5D78)
[Address] EAT @explorer.exe (URLOpenBlockingStreamA) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED8058)
[Address] EAT @explorer.exe (URLOpenBlockingStreamW) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED8138)
[Address] EAT @explorer.exe (URLOpenPullStreamA) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED821C)
[Address] EAT @explorer.exe (URLOpenPullStreamW) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED82E0)
[Address] EAT @explorer.exe (URLOpenStreamA) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED8408)
[Address] EAT @explorer.exe (URLOpenStreamW) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED84D0)
[Address] EAT @explorer.exe (UnregisterWebPlatformPermanentSecurityManager) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E7C9B4)
[Address] EAT @explorer.exe (UrlMkBuildVersion) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67EA2804)
[Address] EAT @explorer.exe (UrlMkGetSessionOption) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E33E60)
[Address] EAT @explorer.exe (UrlMkSetSessionOption) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E5D0E4)
[Address] EAT @explorer.exe (UrlmonCleanupCurrentThread) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67E4A27C)
[Address] EAT @explorer.exe (WriteHitLogging) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED85D0)
[Address] EAT @explorer.exe (ZonesReInit) : MrmCoreR.dll -> HOOKED (C:\WINDOWS\system32\urlmon.dll @ 0x67ED9C30)
[Address] EAT @explorer.exe (AccConvertAccessMaskToActrlAccess) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AEFA0C)
[Address] EAT @explorer.exe (AccConvertAccessToSD) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AEFB80)
[Address] EAT @explorer.exe (AccConvertAccessToSecurityDescriptor) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AEFD3C)
[Address] EAT @explorer.exe (AccConvertAclToAccess) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AEFE90)
[Address] EAT @explorer.exe (AccConvertSDToAccess) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AEFF2C)
[Address] EAT @explorer.exe (AccFreeIndexArray) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AE0D80)
[Address] EAT @explorer.exe (AccGetAccessForTrustee) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AF01A8)
[Address] EAT @explorer.exe (AccGetExplicitEntries) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AF0288)
[Address] EAT @explorer.exe (AccGetInheritanceSource) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AE0EA0)
[Address] EAT @explorer.exe (AccLookupAccountName) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AF0348)
[Address] EAT @explorer.exe (AccLookupAccountSid) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AF0648)
[Address] EAT @explorer.exe (AccLookupAccountTrustee) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AF09CC)
[Address] EAT @explorer.exe (AccProvCancelOperation) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AECAFC)
[Address] EAT @explorer.exe (AccProvGetAccessInfoPerObjectType) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AECB74)
[Address] EAT @explorer.exe (AccProvGetAllRights) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AECC1C)
[Address] EAT @explorer.exe (AccProvGetCapabilities) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AD8100)
[Address] EAT @explorer.exe (AccProvGetOperationResults) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AECDF8)
[Address] EAT @explorer.exe (AccProvGetTrusteesAccess) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AECF38)
[Address] EAT @explorer.exe (AccProvGrantAccessRights) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AED040)
[Address] EAT @explorer.exe (AccProvHandleGetAccessInfoPerObjectType) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AED1B0)
[Address] EAT @explorer.exe (AccProvHandleGetAllRights) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AED298)
[Address] EAT @explorer.exe (AccProvHandleGetTrusteesAccess) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AED410)
[Address] EAT @explorer.exe (AccProvHandleGrantAccessRights) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AEC4D0)
[Address] EAT @explorer.exe (AccProvHandleIsAccessAudited) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AED48C)
[Address] EAT @explorer.exe (AccProvHandleIsObjectAccessible) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AED524)
[Address] EAT @explorer.exe (AccProvHandleRevokeAccessRights) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AED660)
[Address] EAT @explorer.exe (AccProvHandleRevokeAuditRights) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AED738)
[Address] EAT @explorer.exe (AccProvHandleSetAccessRights) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AED810)
[Address] EAT @explorer.exe (AccProvIsAccessAudited) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AED910)
[Address] EAT @explorer.exe (AccProvIsObjectAccessible) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AEDA24)
[Address] EAT @explorer.exe (AccProvRevokeAccessRights) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AEDE74)
[Address] EAT @explorer.exe (AccProvRevokeAuditRights) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AEDFB0)
[Address] EAT @explorer.exe (AccProvSetAccessRights) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AEE0EC)
[Address] EAT @explorer.exe (AccRewriteGetExplicitEntriesFromAcl) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AD7BD4)
[Address] EAT @explorer.exe (AccRewriteGetHandleRights) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AE1510)
[Address] EAT @explorer.exe (AccRewriteGetNamedRights) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AE1680)
[Address] EAT @explorer.exe (AccRewriteSetEntriesInAcl) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AD3070)
[Address] EAT @explorer.exe (AccRewriteSetHandleRights) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AD2270)
[Address] EAT @explorer.exe (AccRewriteSetNamedRights) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AD3BA0)
[Address] EAT @explorer.exe (AccSetEntriesInAList) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AF0AD4)
[Address] EAT @explorer.exe (AccTreeResetNamedSecurityInfo) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AD58A0)
[Address] EAT @explorer.exe (EventGuidToName) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69ADDE68)
[Address] EAT @explorer.exe (EventNameFree) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69ADDEF4)
[Address] EAT @explorer.exe (GetExplicitEntriesFromAclW) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AD7BCC)
[Address] EAT @explorer.exe (GetMartaExtensionInterface) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AD3600)
[Address] EAT @explorer.exe (GetNamedSecurityInfoW) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AD2680)
[Address] EAT @explorer.exe (GetSecurityInfo) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AD1390)
[Address] EAT @explorer.exe (SetEntriesInAclW) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AD3060)
[Address] EAT @explorer.exe (SetNamedSecurityInfoW) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AD3E64)
[Address] EAT @explorer.exe (SetSecurityInfo) : wevtapi.dll -> HOOKED (C:\WINDOWS\SYSTEM32\ntmarta.dll @ 0x69AD21B0)
¤¤¤ Externí včelstvo: ¤¤¤
¤¤¤ Nákaza : ¤¤¤
¤¤¤ Soubor HOSTS: ¤¤¤
--> %SystemRoot%\System32\drivers\etc\hosts
¤¤¤ Kontrola MBR: ¤¤¤
+++++ PhysicalDrive0: (\\.\PHYSICALDRIVE0 @ IDE) INTEL SSDSC2CT060A3 +++++
--- User ---
[MBR] f3bfc6ad82f915b2798dfaed686e4a05
[BSP] 813a4c5b36d93f4fde867d8b6de9f9a6 : Windows 7/8 MBR Code
Partition table:
0 - [ACTIVE] NTFS (0x07) [VISIBLE] Offset (sectors): 2048 | Size: 351 MB
1 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 722925 | Size: 56886 MB
User = LL1 ... OK!
User = LL2 ... OK!
+++++ PhysicalDrive1: (\\.\PHYSICALDRIVE1 @ IDE) WDC WD10EZEX-00RKKA0 +++++
--- User ---
[MBR] f29db3fad84b45b4fde704263416408d
[BSP] 57f61b446f7c1919f2d55e5dbad2f0af : Windows 7/8 MBR Code
Partition table:
0 - [XXXXXX] NTFS (0x07) [VISIBLE] Offset (sectors): 2048 | Size: 953866 MB
User = LL1 ... OK!
User = LL2 ... OK!
+++++ PhysicalDrive2: (\\.\PHYSICALDRIVE2 @ USB) Generic- SD/MMC USB Device +++++
Error reading User MBR! ([0x15] Za?ízení není p?ipraveno. )
User = LL1 ... OK!
Error reading LL2 MBR! ([0x32] Po?adavek není podporován. )
+++++ PhysicalDrive3: (\\.\PHYSICALDRIVE3 @ USB) Generic- Compact Flash USB Device +++++
Error reading User MBR! ([0x15] Za?ízení není p?ipraveno. )
User = LL1 ... OK!
Error reading LL2 MBR! ([0x32] Po?adavek není podporován. )
+++++ PhysicalDrive4: (\\.\PHYSICALDRIVE4 @ USB) Generic- SM/xD-Picture USB Device +++++
Error reading User MBR! ([0x15] Za?ízení není p?ipraveno. )
User = LL1 ... OK!
Error reading LL2 MBR! ([0x32] Po?adavek není podporován. )
+++++ PhysicalDrive5: (\\.\PHYSICALDRIVE5 @ USB) Generic- MS/MS-Pro USB Device +++++
Error reading User MBR! ([0x15] Za?ízení není p?ipraveno. )
User = LL1 ... OK!
Error reading LL2 MBR! ([0x32] Po?adavek není podporován. )
Dokončeno : << RKreport[0]_S_05012014_210156.txt >>
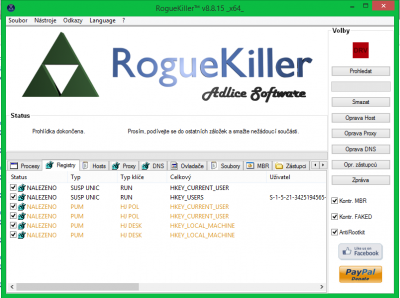
- Pro lepší orientaci přikládám screen programu





